
All the invited business contacts of XS4ALL received a Poken at the registration desk of the FIFI2008 conference. It turned out to be the most interesting object of the day. The main conference theme was internet, society and security and the first session that got my interest was a live demonstration of social engineering by Ruud van Diemen from Fox-IT.
Used chewing gum or USB-stick?
At the registration desk Fox-IT randomly handed out ten USB sticks to conference visitor. During the session van Diemen asked the audience who had received a USB stick. He then asked these people if they would like to trade this USB stick for his used piece of chewing gum. They all declined and they all admitted to having plugged the USB stick into their computers to take a look at the contents. This is one of the ways Fox-IT hacks into people’s systems to test the security of their businesses. It is a smart way to tap into peoples curiosity, especially if you camouflage the USB stick as a panda in the case of Poken.
Do you Poken?
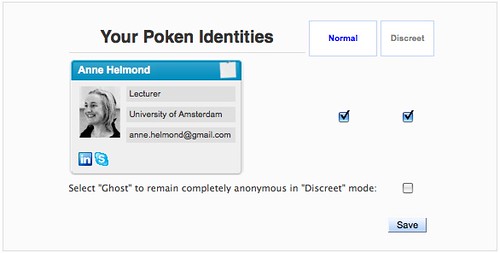
Poken is a new service that both tries to bridge the gap between social networks and at the same time it is a new type of business card.
While I have actually started to like handing out business cards since I’ve got Moo cards one of the things about receiving business cards is that they are piled onto one stack in the corner of my study. It takes me too much time to scan them and use them in Evernote for example. I prefer to keep my contacts online although Plaxo simply isn’t my service. There is another new service that promises to be the future of social networking, (Hello, my name is) E, which has recently rolled out a connector which seems to do the same as Poken, namely exchange your contact details through a small device which you can then plug into your USB port to upload and synchronize.
Unfortunately, E is still very much in beta and the connector is not widely available yet. Poken, on the other hand has recently started to hand out their pokens, and boy are they cute! I was actually pretty surprised when I found out the company is not from Japan because the Pokens just breathe Japanese gadget cuteness. I do think there is a market for both E and Poken because their connectors seem to point to two very different user groups. The Pokens are cute but Do You Poken currently only supports the social networking sites LinkedIn, Facebook and USgang (never heard of) but both Poken and E are expanding their integration with services.

Or is your name E?
The different user groups for both services do not so much show in the currently integrated services but especially in the look and feel of their exchange device, the connector. The Pokens are several cute little animals or ghosts that seem to point to a young target group of teenagers.

On the other hand, the E connector fits a more professional target group with its look and feel that perfectly fits your MacBook or Air.
So what is the future of social networking? I certainly see devices such as directly exchanging contact information by simply touching phones (E) or connectors (E & Poken) as a way to replace business cards. On the other hand, the story of van Diemen about plugging in “strange” USB devices also raises questions about security issues. How vulnerable are such devices?
UPDATE: Timo Arnall wrote a great post on Poken as ‘a physical networking platform, with physical, RFID-based objects.’
Disclaimer: The new media scene in Amsterdam is pretty small, so yes, I do know the people behind E. Keep up the great work!
Do you Poken? via Anne Helmond http://tinyurl.com/56ghdu
Poken – http://is.gd/awRs – Couple of interesting posts – http://is.gd/awQR and http://is.gd/awQZ
Thanks for turning me onto E. Ha.
This should be a fun tool to try out and conferences and smaller get togethers.
E looks great! I can’t wait!
@jillesdotcom Een poken. En deze is zonder spyware? Zie blog @slivertje http://bit.ly/OhNi
@LauraVL Or: http://tinyurl.com/56ghdu (by @silvertje)
Don’t you think poken is sensitive for your privacy and things like virusses and spyware?
Yes, in general, swapping data with USB-sticks is very sensitive to virusses and spyware. It is a matter of time before someone develops spyware for Pokens and the developers must take this into account. On the other hand, users should always protect themselves with anti-spyware software.
In the case of theft, or a lost Poken, the user can register its Poken as lost which will disable the device for further use.